The SAMA Counter-Fraud Framework sets clear, enforceable obligations for every organization operating in the Saudi financial sector. Fintechs, payment service providers, and financial organizations must demonstrate that they can govern, prevent, detect, and respond to fraud — not just in policy documents, but through operating technology and measurable controls. For many organizations, the gap between regulatory intent and operational readiness is still significant.
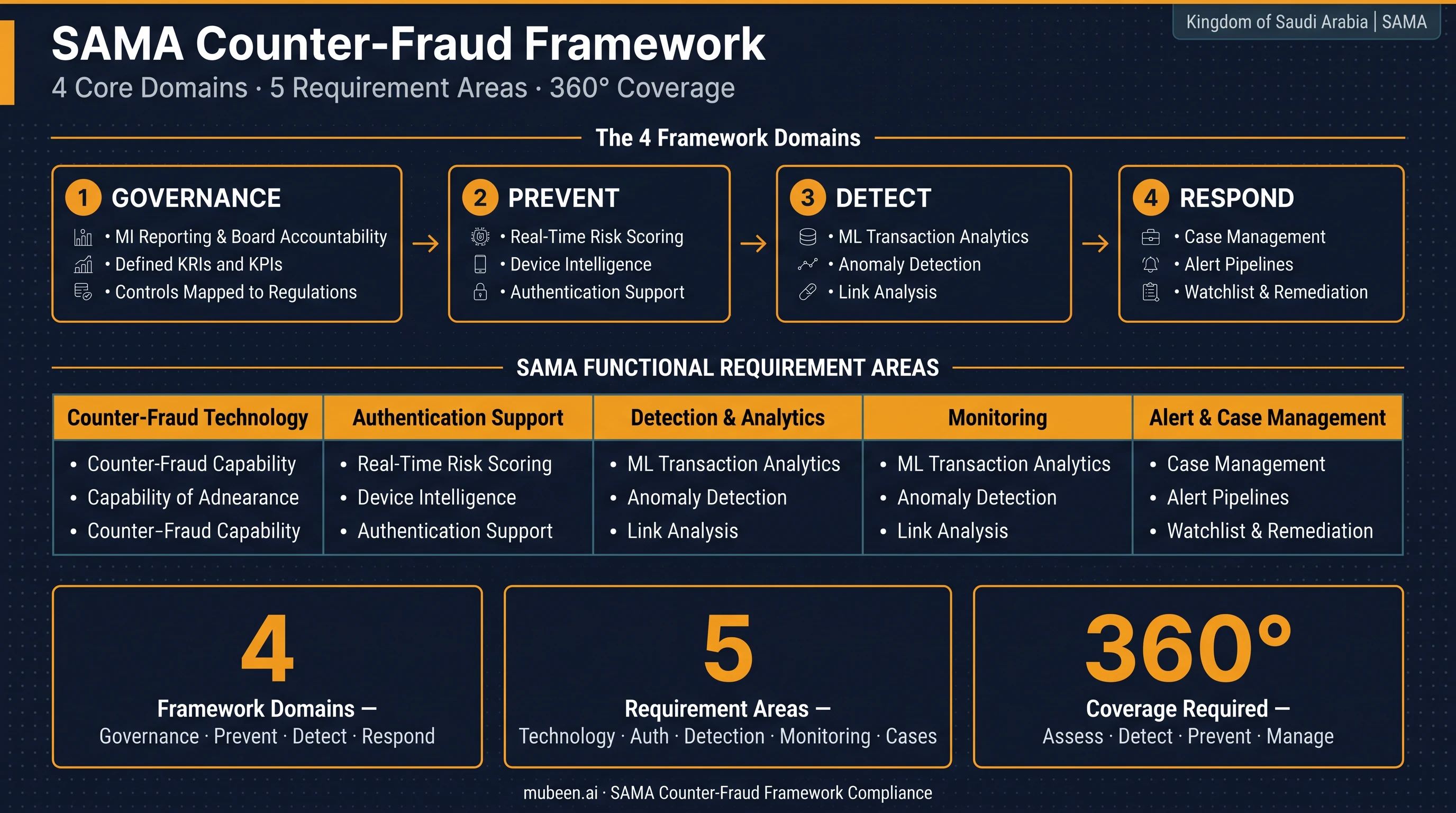
The Four Framework Domains
SAMA structures its counter-fraud requirements around four core domains. Each demands both technical capability and institutional process. Understanding what is required across every domain is the starting point for building a compliant programme.
Governance
Institutions must demonstrate active oversight of fraud risk through MI reporting, defined KRIs and KPIs, training programmes, and explicit mapping of technology controls to regulatory requirements. Governance is not a one-time exercise — SAMA expects continuous measurement and board-level accountability.
Prevent
Prevention covers real-time risk scoring, device intelligence, authentication support, typology monitoring, and preventive rules that stop fraud before transactions complete. This requires technology that acts at the point of interaction, not after the fact.
Detect
Detection demands analytics infrastructure capable of anomaly detection, machine learning on transaction patterns, link analysis across accounts, and continuous monitoring. Static rule sets alone do not meet SAMA's detection expectations.
Respond
Response covers alerting pipelines, case management, structured investigations, evidence capture, watchlist management, and remediation workflows. A detected fraud event that cannot be actioned quickly is a compliance gap.
Mapping Requirements to Technology
Beyond the four domains, SAMA specifies functional requirement areas that institutions must address through their counter-fraud technology stack. The compliance roadmap below shows where each requirement lands and what capability it demands.
| SAMA Requirement | Technology Capability Required |
|---|---|
| Counter-Fraud Technology | Risk engine with configurable rules, explainable scoring, watchlists, velocity controls, and rapid scenario deployment |
| Authentication Support | Fraud signal integration with step-up authentication orchestration for challenged sessions |
| Detection & Analytics | Fraud risk engine, device intelligence feeds, and a fraud monitoring dashboard for analyst visibility |
| Monitoring to Detect Fraud | Transaction scoring, device intelligence, ML-derived payment fraud patterns, and institution-specific custom rules |
| Alert & Case Management | Investigation framework, structured case workflows, and end-to-end case management from alert to resolution |
SAMA does not prescribe specific vendors, but it does expect institutions to demonstrate that their technology actively covers each of these requirement areas — and that controls are mapped, tested, and auditable.
An AI-managed risk engine addresses the counter-fraud technology and detection requirements directly: configurable rules, ML scoring, and explainability are built-in, not bolted on. For authentication support, the same risk signals that score transactions can trigger step-up challenges through your existing authentication provider.
Device intelligence sits across both the prevention and detection domains. At onboarding, it catches emulators and bot-driven fake account creation. In transaction monitoring, it flags session anomalies — devices behaving inconsistently with their historical profile — that rule-based systems miss.
Building Your Counter Fraud Strategy
One of the most common mistakes in compliance programmes is attempting full deployment before any controls are operational. SAMA's framework is complex. Trying to satisfy every requirement simultaneously leads to delayed delivery and gaps in coverage.
A structured, phased approach works better:
- Translate regulatory expectations into an operating model with clear ownership
- Prioritise the highest-risk fraud use cases and existing control gaps first
- Develop monitoring, investigations, watchlists, and reporting workflows in parallel
- Start in alert-only mode to calibrate thresholds, then phase into blocking controls
This sequencing means your organization begins generating compliance evidence — alert data, case records, KPI reporting — before the full programme is complete. A fraud resilience assessment can accelerate this by identifying which gaps carry the highest regulatory and financial risk, so effort is focused where it matters most.
For payment transaction fraud, the monitoring and detection requirements are particularly demanding. ML-derived fraud patterns must cover real-time card, transfer, and digital wallet transactions — not just batch-reviewed reports. AML compliance adds another layer: the same transaction monitoring infrastructure must surface suspicious activity patterns reportable to SAFIU.
The risk analytics dashboard ties the operational picture together, giving fraud teams real-time visibility into alert volumes, case status, and KPI metrics that governance reporting requires.
Key Takeaways
- SAMA's Counter-Fraud Framework requires coverage across four domains — Governance, Prevent, Detect, and Respond — not just detection technology
- Five functional requirement areas must be mapped to specific technology capabilities, with controls that are auditable and explainable
- A phased approach — prioritising high-risk use cases first and starting in alert-only mode — delivers earlier compliance evidence and reduces implementation risk
- Device intelligence and ML-based scoring are central to both the prevention and detection domains; static rules alone do not meet SAMA's expectations
- Governance reporting requires live KPI data, which means case management and dashboarding infrastructure must be operational, not just planned
SAMA's counter-fraud programme is designed to raise the floor across the entire Saudi financial sector. Organizations that treat it as a technology procurement exercise will struggle; those that build a structured operating model — with technology, process, and governance aligned — will find compliance and fraud reduction reinforce each other. For a plain-language breakdown of what the framework requires, see SAMA counter fraud: meaning and core requirements.